"Executive Summary Security Policy Management Zero Trust Security Market Size and Share Forecast
CAGR Value
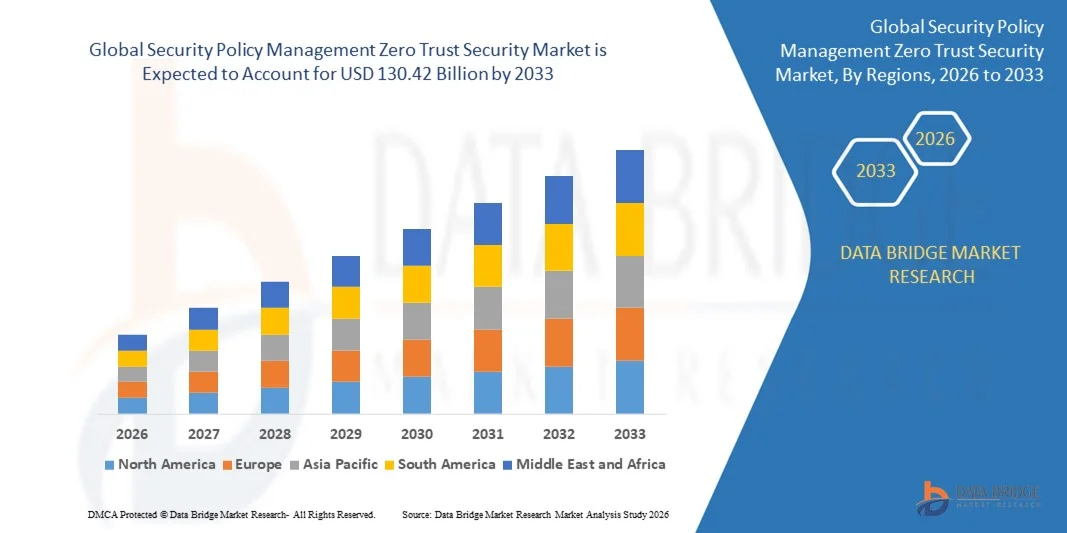
- The global Security Policy Management Zero Trust Security Market size was valued at USD 42.04 billion in 2025 and is projected to reach USD 130.42 billion by 2033, growing at a CAGR of 15.20% during the forecast period.
Security Policy Management Zero Trust Security Market report works very well for initiating and enhancing the strategies for sales, advertising, marketing, and promotion. SWOT analysis has been applied in the report, which highlights the global key manufacturers, market definition, description, and analysis of the market competition landscape along with many other factors. Competitor strategies such as new product launches, expansions, agreements, joint ventures, partnerships, and acquisitions help the keyword market industry to take better steps for selling goods and services. Security Policy Management Zero Trust Security Market Research Report has the best answers to many of the critical business questions and challenges.
To make this Security Policy Management Zero Trust Security report of supreme quality, consistent efforts of enthusiastic, dynamic, and skilled researchers and analysts have been utilized. This results in actionable ideas, better decision-making, and better business strategies. It simplifies the flow of information for better user understanding. The most appropriate, unique, and credible global market research report has been brought to valuable customers and clients depending upon their specific business needs. Besides, the market share of major competitors on a global level is also studied, where key areas such as Europe, North America, Asia Pacific, and South America are taken into account in this Security Policy Management Zero Trust Security Market research report.
Gain clarity on industry shifts, growth areas, and forecasts in our Security Policy Management Zero Trust Security Market report. Get your copy:
https://www.databridgemarketresearch.com/reports/global-security-policy-management-zero-trust-security-market
Security Policy Management Zero Trust Security Market Review
Segments
- Component: The market can be segmented based on components such as solution and services. Zero trust security solutions encompass various tools and technologies to ensure secure access and prevent unauthorized breaches. On the other hand, services include consulting, integration, and support services for seamless implementation and management of zero trust security policies.
- Deployment Mode: This segment categorizes the market based on deployment modes like cloud-based and on-premises solutions. With the increasing adoption of cloud computing, many organizations are opting for cloud-based zero trust security solutions for better scalability and flexibility.
- Organization Size: The market can also be segmented based on organization size, including small and medium-sized enterprises (SMEs) and large enterprises. Zero trust security policies are crucial for organizations of all sizes to protect their sensitive data and prevent cyber threats effectively.
- Vertical: Vertical segmentation is based on industry verticals such as BFSI, healthcare, IT and telecom, government, and others. Each industry has unique security requirements, and zero trust security policies can be tailored to meet specific industry standards and compliance regulations.
Market Players
- Cisco Systems, Inc.: Cisco offers a comprehensive zero trust security solution that integrates network security, access control, and threat protection to provide a robust defense mechanism against cyber threats.
- Palo Alto Networks, Inc.: Palo Alto Networks is known for its advanced security platforms that include zero trust capabilities to secure networks, endpoints, and cloud environments effectively.
- Symantec Corporation: Symantec provides a range of security solutions, including zero trust security features, to help organizations defend against advanced cyber threats and secure sensitive data.
- Check Point Software Technologies Ltd.: Check Point offers advanced threat prevention technologies that can be integrated into zero trust security frameworks to enhance overall cybersecurity posture.
- Microsoft Corporation: Microsoft provides zero trust security solutions that leverage its Azure cloud platform and integrated security features to protect organizations from evolving cyber threats.
The global security policy management zero trust security market is witnessing significant growth due to the rising concerns over cybersecurity threats and the need for stringent access controls in enterprise environments. Factors such as the increasing adoption of cloud services, the proliferation of mobile devices, and the growing sophistication of cyber attacks are driving the demand for robust security policy management solutions. Organizations are increasingly realizing the importance of implementing zero trust security frameworks to prevent unauthorized access and protect critical data assets. The market is highly competitive, with key players investing in research and development to offer advanced security solutions that cater to evolving cybersecurity challenges and regulatory requirements.
The global security policy management zero trust security market is experiencing a transformational shift as organizations increasingly prioritize data protection and cybersecurity measures in response to a surge in cyber threats and attacks. One of the emerging trends in the market is the integration of artificial intelligence (AI) and machine learning (ML) technologies into zero trust security solutions. AI and ML capabilities enable organizations to enhance threat detection, automate security protocols, and adapt to evolving cyber threats in real-time, thereby strengthening their overall security posture.
Another key trend shaping the market is the emphasis on user-centric security approaches within zero trust frameworks. As traditional perimeter-based security measures prove inadequate in today's dynamic threat landscape, organizations are focusing on identity-based security models that authenticate and authorize users based on granular levels of trust. User behavior analytics, multi-factor authentication, and continuous monitoring are integral components of user-centric zero trust security strategies that prioritize individual user identities rather than network perimeters.
Furthermore, the market is witnessing a convergence of zero trust security with other cybersecurity technologies such as Secure Access Service Edge (SASE) and Extended Detection and Response (XDR) solutions. This convergence enables organizations to streamline their security operations, simplify management complexities, and achieve holistic visibility and control across their network, cloud, and endpoint environments. By integrating zero trust principles with SASE and XDR technologies, organizations can establish a unified security fabric that safeguards against a wide range of cyber threats and vulnerabilities.
The rising adoption of zero trust security frameworks across industry verticals is fueling the demand for specialized zero trust security vendors that offer tailored solutions for specific sectors. Vertical-specific security requirements in industries such as healthcare, finance, and government necessitate customized zero trust approaches that address sector-specific compliance mandates and regulatory standards. Vendors that can demonstrate expertise in addressing industry-specific security challenges are poised to capitalize on the growing demand for specialized zero trust security solutions.
In conclusion, the global security policy management zero trust security market is evolving rapidly to meet the complex security needs of modern organizations in the face of escalating cyber threats. By embracing AI-powered security analytics, user-centric security paradigms, and strategic technology integrations, organizations can fortify their defenses, mitigate risks, and enhance their overall resilience in a cybersecurity landscape plagued by increasingly sophisticated threats. The market outlook for zero trust security remains promising, driven by the imperative for organizations to adopt proactive and adaptive security measures that align with the principles of zero trust to safeguard their digital assets and data integrity effectively.The global security policy management zero trust security market is experiencing a paradigm shift driven by the escalating cyber threats and attacks that are compelling organizations to prioritize data protection and cybersecurity measures. One emerging trend in the market is the integration of AI and ML technologies into zero trust security solutions. This integration enables organizations to enhance threat detection capabilities, automate security protocols, and adapt to evolving cyber threats in real-time, thereby strengthening their overall security posture. By leveraging AI and ML, organizations can achieve proactive threat mitigation and establish more robust defenses against sophisticated cyber attacks.
Another key trend shaping the market is the transition towards user-centric security approaches within zero trust frameworks. With traditional perimeter-based security measures proving insufficient in combating modern cyber threats, organizations are shifting towards identity-based security models that focus on authenticating and authorizing users based on granular levels of trust. User behavior analytics, multi-factor authentication, and continuous monitoring are pivotal components of user-centric zero trust security strategies that prioritize individual user identities over network perimeters. This user-centric approach enhances security by ensuring that access controls are tailored to the specific needs and behaviors of individual users, thereby reducing the risk of unauthorized access and data breaches.
Moreover, the market is witnessing a convergence of zero trust security with other cybersecurity technologies such as Secure Access Service Edge (SASE) and Extended Detection and Response (XDR) solutions. This strategic convergence empowers organizations to streamline their security operations, simplify management complexities, and achieve comprehensive visibility and control across their network, cloud, and endpoint environments. By combining zero trust principles with SASE and XDR technologies, organizations can establish a unified security framework that effectively safeguards against a wide array of cyber threats and vulnerabilities. This integrated approach enhances the overall security posture of organizations by ensuring seamless coordination and communication between different security tools and technologies.
In conclusion, the evolving landscape of the global security policy management zero trust security market is characterized by dynamic trends that underscore the industry's shift towards more sophisticated and holistic security solutions. By embracing AI-powered security analytics, user-centric security paradigms, and strategic technology integrations, organizations can bolster their cybersecurity defenses, mitigate risks, and enhance their resilience against evolving cyber threats. The market outlook for zero trust security remains promising as organizations increasingly recognize the imperative of implementing proactive and adaptive security measures aligned with the principles of zero trust to safeguard their digital assets and data integrity effectively.
Uncover the company’s portion of market ownership
https://www.databridgemarketresearch.com/reports/global-security-policy-management-zero-trust-security-market/companies
Structured Market Research Questions for Security Policy Management Zero Trust Security Market
- What is the present size of the global Security Policy Management Zero Trust Security industry?
- What annual growth rate is projected for the Security Policy Management Zero Trust Security sector?
- What are the main segment divisions in the Security Policy Management Zero Trust Security Market report?
- Who are the established players in the global Security Policy Management Zero Trust Security Market?
- What geographic areas are explored in the Security Policy Management Zero Trust Security Market report?
- Who are the leading manufacturers and service providers for Security Policy Management Zero Trust Security Market?
Browse More Reports:
Global Holter ECG Market
Global Hot Fill Packaging Market
Global Hurthle Cell Carcinoma Treatment Market
Global Hybrid Integration Platform Market
Global Hybrid Valve Market
Global Hydrochloric Acid Market
Global Hydronephrosis Market
Global Hydroponic Under-floor Heating Systems Market
Global Hygiene Breathable Films Market
Global Hypodermic Needles Market
Global Idler Arm Market
Global Inactivated Vaccines Market
Global Indigo Carmine Market
Global Industrial Hearable Market
Global Industrial Nailer Market
About Data Bridge Market Research:
An absolute way to forecast what the future holds is to comprehend the trend today!
Data Bridge Market Research set forth itself as an unconventional and neoteric market research and consulting firm with an unparalleled level of resilience and integrated approaches. We are determined to unearth the best market opportunities and foster efficient information for your business to thrive in the market. Data Bridge endeavors to provide appropriate solutions to the complex business challenges and initiates an effortless decision-making process. Data Bridge is an aftermath of sheer wisdom and experience which was formulated and framed in the year 2015 in Pune.
Contact Us:
Data Bridge Market Research
US: +1 614 591 3140
UK: +44 845 154 9652
APAC : +653 1251 975
Email:- corporatesales@databridgemarketresearch.com
"